An Efficient Bio-key Management Scheme for Telemedicine Applications
An Efficient Bio-key Management strategy for Telemedicine Applications
Abstraction: Checkup detector webs play a critical function for real-time wellness attention monitoring of telemedicine based applications. Telemedicine provide specialized health care audience to patients in distant locations. We use electronic information and communicating engineerings to supply and back up health care when the distance separate the participants. In order to guarantee the privateness and security of patient’s critical wellness information, it is indispensable to supply efficient cryptanalysis strategy. This paper presents a fresh Mamdani based Bio-Key Management ( MBKM ) technique, which assures existent clip wellness attention supervising with out any overhead. We present the simulation consequences to demo that the proposed MBKM strategy can accomplish greater security in footings of public presentation prosodies such as False Match Rate ( FMR ) , False Non Match Rate ( FNMR ) , and Genuine Acceptance Rate ( GAR ) than other recent bing attacks.
Keywords:Healthcare, security, Medical detector webs, Key Management
Order custom essay An Efficient Bio-key Management Scheme for Telemedicine Applications with free plagiarism report
 450+ experts on 30 subjects
450+ experts on 30 subjects
 Starting from 3 hours delivery
Starting from 3 hours delivery
1. Introduction
Progresss in communicating engineerings, such as wearable and implantable biosensors, along with recent developments in the embedded computer science country are enabling the design, development, and execution of medical detector webs. This category of webs is paving the manner for the deployment of advanced health care monitoring applications. In the past few old ages, much of the research in the country of medical detector webs has focused on issues related to medical detector designs, detector miniaturisation, low-power detector circuitry, signal processing, and communications protocols. In this paper, we present a novel Mamdani based Bio-Key Management ( MBKM ) , which assures existent clip wellness attention supervising with less operating expense for telemedicine applications. Telemedicine means the distant medical expertness at the point of demand or medicate at distance. Telemedicine engineering is chiefly required for the people populating in rural countries, aged people and handicapped people [ 1 ] . We highlight some of the design challenges and unfastened issues that still need to be addressed to do medical detector webs genuinely everyplace.
The development of telemedicine based health care applications presents assorted fresh challenges like dependable existent clip informations transportation, seasonableness, Energy and Power direction for a broad scope of applications [ 2 ] . Further using new engineerings in telemedicine applications without sing security facets like privateness, hallmark, confidentiality and unity as susceptible [ 3 ] . For illustration, the patient’s wellness information is delicate and escape of single patient’s personal informations could do him uncomfortable. Furthermore sometimes exposing wellness information may ensue in a individual losing his occupation or do it infeasible to obtain insurance protection [ 4 ] .
Fig.1 explains the hazards to patient security in Body Area Network ( BAN ) . Here assorted detectors are implanted in the human organic structure to mensurate the critical marks like ECG, EEG, EMG, Blood force per unit area, glucose degree, etc. , can be connected to other detectors or to the control nodes. Further detectors transmit the patient information to a medical expertness utilizing wired or wireless engineering. Now the interloper may spy the patient informations and he can change or may post the information in societal sites, which pose hazards to patient’s security.
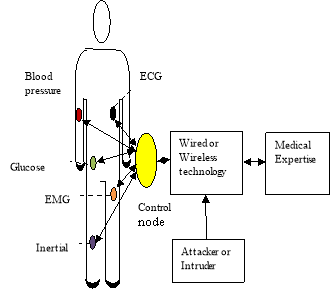
Fig.1 Risks to patient security
More significantly, Healthcare supplier must follow HIPAA ( Health Insurance Portability and Accountability Act ) regulations. Otherwise supplier is subjected to punishment [ 5 ] .So a patient security is a most of import anxiousness in telemedicine based health care applications.
2. Related Plants
With the betterment of progress engineering invasive computer science is observed as cardinal engineering to help streaming medical informations communicating for telemedicine based applications with the aid of deploying detectors [ 6, 7 ] .Several solutions for medical information security have been proposed to protect the Body country web security. ECC ( Elliptic curve cryptanalysis ) , hardware encoding, TinySec and biometric methods are sorts of solutions discussed in [ 8 ] . Link layer encoding is achieved in the organic structure country web by TinySec attack [ 9 ] . If one medical detector releases the key or it acts as an aggressor, all the information in the Body country web will be released. Elliptic curve cryptanalysis ( ECC ) has been used in the radio detector webs [ 10, 11 ] . This public cardinal cryptographic technique requires more energy compared to symmetric cardinal cryptanalytic techniques.
Biometricss obtained from the human organic structure to procure the key is proposed in [ 12 ] . Compared with cryptanalytic techniques, this technique cut down calculation and communicating cost. Electro cardio gm ( ECG ) and Photo plethysmogram ( PPG ) signals are used as first-class biometric characteristics to procure the informations in organic structure country web [ 13, 14 ] .
The fuzzed vault strategy has been preponderantly used for biometric hallmark, such as fingerprints and iris image acknowledgment [ 15–17 ] . Fuzzy vault strategy play a major function to work out the job of security in telemedicine based applications. Fuzzy vault strategy is used in Phsiological Signal based Key Agreement ( PSKA ) to set up secured pairwise cardinal understanding between the nodes in Body country webs [ 18 ] , which solves chiefly the synchronism job and issues in characteristic reordering [ 19 ] .
Biometric Encryption strategy is a cryptanalysis strategy which is used to keep the security of biometries and bring forth a strong key from biometries [ 20 ] . In this strategy, the husk points are non necessary to be added to convey, so the hold clip and energy ingestion is reduced.
In [ 21 ] , the writer proposes new thought for message and user hallmark. This strategy compares present ECG signal with the antecedently recorded ECG templet to verify the individuality. Since the templet is inactive, this method provides hapless public presentation. The writers of the paper [ 22 ] propose ECG-IJS strategy to better hallmark of streaming medical information. The writer used characteristics of ECG signal to identify coevals for unafraid real-time medical informations communicating.
3. System Design
Mamdani based Bio-key Management ( MBKM ) strategy is proposed based on the earlier treatment on ECG-IJS strategy. MBKM strategy is introduced to guarantee the security for streaming medical informations communicating in Telemedicine based applications. The proposed MBKM strategy is shown in Fig. 2.






























Fig. 2 MBKM strategy
A novel proposed MBKM strategy is shown in Fig. 2 which uses organic structure country webs to give qui vive to the infirmary, even before the patient have critical jobs like bosom onslaught, glucose degree through mensurating alterations in their important marks as temperature of the patient, pulse rate, glucose degree, blood force per unit area and respiratory rate. Detectors, which are implanted in the patient’s organic structure step the degree of important marks and convey the parametric quantity values to medical expert working in the intensive bearer unit of the infirmary to take necessary actions to salvage the life of a patient.
Intensive attention units are equipped with multi-modal proctors which are able to simultaneously step and expose the wellness position of the patient. In such instance, this important real-time medical information must be good sheltered against aggressors and security facets must be satisfied [ 23 ] . Health attention units with hapless security execution processs for telemedicine may take to incorrect diagnosing and intervention for the patient.
The process at the transmitter side is given as follows: Electrocardiogram detector is used to detect the ECG signal from the human organic structure. Nyquist theorem at the rate of 120 Hz is applied on the ECG signal to take samples. 512 points Fast Fourier transform ( FFT ) is conducted on the sampled ECG informations. Since FFT procedure is symmetric foremost 256 coefficients are retained among 512 coefficients. All the extremum values on the extracted FFT coefficients are used as characteristics. A multinomial equation with degree N is constructed and the cardinal K is generated. Patient’s information is encrypted with the generated key K and hash value based on SHA-1 algorithm is calculated. Then sender sends the envelope contains the encrypted message, subset of coefficients and hash value to the receiving system.
The process at the receiver side is described as follows: Similar to the transmitter, receiving system besides repeats the process to detect the ECG signal, try the signal and pull out the first 256 Feature coefficients. Then a new multinomial with degree M is constructed utilizing the standard coefficients and the multinomial on all points in characteristics to acquire a set of braces. Key at the receiving system K’ is reconstructed from received coefficients and the new hash value is calculated. Key K and hash value is compared with reconstructed cardinal K’ and new hash value. If the keys are same, so decrypted information is authenticated informations.
Mamdani based Fuzzy illation system is playing a major function to guarantee security in telemedicine applications. Stairss for the design of fuzzed illation system are explained in the instance of multinomial grade 10 as follows: 1 ) Input signal variables are identified as I1, I2and end product variable is identified as Y. 2 ) Universe of discourse for the input variables are defined in the scope [ -0.01, -1e-16] and end product variable is defined in the scope [ 0,1 ] . 3 ) Linguistic label assigned for the interval pned by each input variables in to a figure of fuzzed subsets are taken as S1, S2, S3, S4, S5,Second6, S7, S8, S9, S10. Linguistic label assigned for the interval pned by each end product variables in to a figure of fuzzed subsets are taken as Yttrium1, Y2, Y3, Y4, Y5Yttrium6, Y7, Y8, Y9, Y104 ) Triangular rank map is assigned for each fuzzy subset. 5 ) Rule-base is formed by delegating the fuzzy relationship between inputs fuzzed subsets on the one manus and end products fuzzy subset on the other manus. If I1is S1and I2is S1so Y is Y1.If I1is S1and I2is S2so Y is Y2.If I1is S1and I2is S3so Y is Y3.If I1is S1and I2is S4so Y is Y4.If I1is S1and I2is S5so Y is Y5.If I1is S1and I2is S6so Y is Y6.If I1is S1and I2is S7so Y is Y7.If I1is S1and I2is S8so Y is Y8.If I1is S1and I2is S9so Y is Y9.If I1is S1and I2is S10so Y is Y10.In similar manner, wholly the 100 combinations of regulations are formed. 6 ) Fuzzy end products recommended by each regulation are aggregated. 7 ) Crisp end product is obtained by using one of the defuzzification technique called Centroid of country ( COA ) . Then utilizing this end product, parametric quantities like False Match Rate, False Non Match Rate and Genuine Acceptance Rate are calculated.
4. Simulation Consequences
We validate the MBKM strategy by mensurating the parametric quantities like False Match Rate ( FMR ) , False Non Match Rate ( FNMR ) and Genuine Acceptance Rate ( GAR ) and Half Total Error Rate ( HTER ) . For this strategy, we downloaded 10 patient’s ECG signal for 10 seconds from MIT-BIH Arrhythmia database. We used MATLAB package tool to imitate the proposed MBKM strategy. ECG signals are used for coevals of cardinal and medical information like EEG, EMG, blood glucose degree, blood force per unit area degree etc. , can be send to medical expertness in existent clip for telemedicine based applications.
The public presentation of FMR versus figure of patients is given inFig. 3. FMR value represents the chance that the system falsely matches the input form to a non-matching templet in the database. It measures the per centum of invalid inputs which are falsely accepted. So FMR value must be low for the stable system. This secret plan proves that False Match Rate is lower in the proposed MBKM strategy when compared to ECG-IJS strategy.

Fig. 3 FMR versus Number of patients
The public presentation of FNMR versus figure of patients is shown inFig. 4. FNMR value represents the chance that the system fails to observe a lucifer between the input form and a duplicate templet in the database. It measures the per centum of valid inputs which are falsely rejected.Stable system should give lower FNMR. This secret plan proves that False Non Match Rate is lower in the proposed MBKM strategy when compared to bing ECG-IJS strategy.
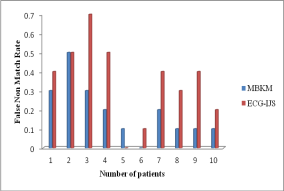
Fig. 4 FNMR versus Number of patients
The public presentation of GAR versus figure of patients is present inFig. 5.GAR value represents the fraction of hallmark efforts by echt users that are accepted. Stable system should give higher GAR. This secret plan proves that Genuine Acceptance Rate is higher in the proposed MBKM strategy when compared to the bing ECG-IJS strategy.
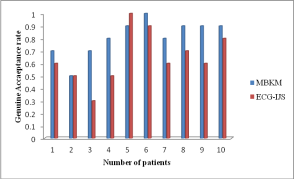
Fig. 5 GAR versus Number of patients
The public presentation of HTER versus figure of patients is present inFig. 6.HTER value represents the norm of False Match Rate and False Non Match Rate. Stable system should give low HTER. This secret plan proves that HTER is lower in the proposed MBKM strategy when compared to the bing ECG-IJS strategy.
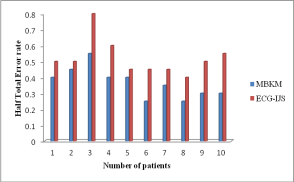
Fig. 6 HTER versus Number of patients
5. Decision
Secure communicating is robustly required to continue a patient’s wellness privateness and safety in telemedicine based applications. In this paper, we present an efficient Mamdani based Bio-Key Management ( MBKM ) strategy for cardinal direction based security strategy in telemedicine based applications. This strategy makes the system stable system by supplying low FNMR, High GAR, low FMR and low HTER. This new strategy is less complex and is offers the security in footings of hallmark, informations confidentiality, informations unity. It remains future work to make energy analysis and implement nervous web attack to procure medical informations communicating for telemedicine applications.
Mentions:
[ 1 ] Yasumitsu Tomaika, Isao Nakajima, Hiroshi Juzoji, Toshihikonkitano, Patent Issues on Telemedicine in eHealth, IEEE International conference on e-Health Networking, Applications and Service,187-193,2008.
Pardeep kumar and Hoon Jay-Lee, Security Issues in Healthcare Applications Using Wireless Medical Sensor Networks: A Survey, Sensors,55-91,2012
[ 3 ] Dimitriou, T. , ,Loannis, K. , Security Issues in Biomedical Wireless Sensor Networks. In Proceedings of 1st International Symposium on Applied Sciences on Biomedical and Communication Technologies ( ISABEL’08 ) , Aalborg, Denmark, 25–28 October 2008.
[ 4 ] Meingast.M, Roosta.T. , Sastry.S, Security and Privacy Issues with Healthcare Information Technology. In Proceedings of the 28th IEEE EMBS Annual International Conference, New York, NY, USA,5453-5458, 31 August–3 September 2006.
. [ 5 ] Office for Civil Rights, United State Department of Health and Human Services. Medical Privacy. National Standards of Protect the Privacy of Personal-Health-Information. Available online: hypertext transfer protocol: //www.hhs.gov/ocr/privacy/hipaa/administrative/privacyrule/index.html.
[ 6 ] J. Woods, “The five manners of centripetal applications, ” Gartner Research, 2006.
[ 7 ] M. M. M. B. Amer and M. I. M. Izraiq, “System with intelligent cable-less transducers for monitoring and analysing biosignals, ” European Patent Application, 2007.
[ 8 ] M. Mana, M. Feham, and B. A. Bensaber, “Trust cardinal direction strategy for radio organic structure country webs, ” International Journal of Network Security, vol. 12, no. 2, pp. 61–69, 2011.
[ 9 ] C. Karlof, N. Sastry, and D. Wagner, “TinySec: a nexus bed security architecture for radio detector webs, ” in Proceedings of the 2nd International Conference on Embedded Networked Sensor Systems, ( SenSys ’04 ) , pp. 162–175, Baltimore, Md, USA, November 2004.
[ 10 ] M. Guennoun, M. Zandi, and K. El-Khatib, “On the usage of biometries to procure radio biosensor webs, ” inProceedings of the 3rd International Conference on Informationand Communication Technologies: FromTheory to Applications, ( ICTTA ’08 ), pp. 1–5, Damascus, Syria, April 2008.
[ 11 ] P. Szczechowiak, L. B. Oliveira, M. Scott, M. Collier, and R. Dahab, “NanoECC: proving the bounds of elliptic curve cryptanalysis in detector webs, ” inProceedings of the 5ThursdayEuropean Conference onWireless Sensor Networks, pp. 305–320, Bologna, Italy, February 2008.
[ 12 ] S. Cherukuri, K. K. Venkatasubramanian, and S. K. S. Gupta, “BioSec: a biometric based attack for procuring communicating in wireless webs of biosensors implanted in the human organic structure, ” inProceedings of the International Conferenceon Parallel Processing Workshops, pp. 432–439, Kaohsiung, Taiwan, October 2003.
[ 13 ] C. C. Y. Poon, Y.-T. Zhang, and S.-D. Bao, “A novel biometries method to procure radio organic structure country detector webs for telemedicine and m-health, ” IEEE Communications Magazine, vol. 44, no. 4, pp. 73–81, 2006.
[ 14 ] S. D. Bao, C. C. Y. Poon, L. F. Shen, and Y. T. Zhang, “Using the timing information of pulse as an entity identifier to procure organic structure detector web, ” IEEE Transactions on Information Technology in Biomedicine, vol. 12, no. 6, pp.772–779, 2008.
[ 15 ] U. Uludag, S. Pankanti, and A. K. Jain, “Fuzzy vault for fingerprints, ” in Proceedings of the Audio- and Video-Based Biometric Person Authentication ( AVBPA ’05 ) , vol. 3546, pp. 310–319, Hilton Rye Town, NY, USA, July 2005.
[ 16 ] E. S. Reddy and I. R. Babu, “Authentication utilizing fuzzed vault based on iris textures, ” inProceedings of the 2nd Asia International Conference on Modelling and Simulation, ( AMS ’08 ), pp. 361–368, Kuala Lumpur, Malaysia, May 2008.
[ 17 ] A. Juels and M. Sudan, “A fuzzy vault strategy, ” inProceedings of the International Symposium on Information Theory, vol. 38, pp. 237–257, Seattle, Wash, USA, July 2006.
[ 18 ] K. K. Venkatasubramanian, A. Banerjee, and S. K. S. Gupta, “PSKA: useable and unafraid cardinal understanding strategy for organic structure country webs, ”IEEE Transactions on Information Technology in Biomedicine, vol. 14, no. 1, pp. 60–68, 2010.
[ 19 ] F. M. Bui and D. Hatzinakos, “Biometric methods for secure communications in organic structure sensor webs: resource-efficient cardinal direction and signal-level informations scrambling, ”EURASIPJournal on Advances in Signal Processing, vol. 2008, Article ID
529879, 16 pages, 2008.
[ 20 ] A. K. Jain, K. Nandakumar, and A. Nagar, “Biometric templet security, ”EURASIP Journal on Advances in Signal Processing, vol. 2008, Article ID 579416, 17 pages, 2008.
[ 21 ] L.Biel, O.Pettersson, L.Philipson and P.Wide.ECG Analysis: A new attack in human designation [ J ] .IEEE Trans.Instrum.Meas,2001:808-812.
[ 22 ] Zhaoyangzhang, Honggangwang, Athanasios V.Vasilokas And Hua Fang.ECG-Cryptography and Authentication in Body Area Networks [ J ] .IEEE Transactions on Information Technology in Biomedicine,2012:1070-1078.
[ 23 ] H.Wang, D.Peng, W.Wang, H.Sharif, H.Hwa Chen and A.Khoynezhad.Resource-aware secure ECG wellness attention supervising through organic structure detector webs [ J ] .IEEEWirelessCommunications,2010: vol.17, no.1,12-19.
Cite this Page
An Efficient Bio-key Management Scheme for Telemedicine Applications. (2018, Aug 20). Retrieved from https://phdessay.com/an-efficient-bio-key-management-scheme-for-telemedicine-applications/
Run a free check or have your essay done for you


